Online Divorce in Virginia: A Step-by-Step Guide...
«I got a divorce, and I felt like I finally started my career. I started making movies ...
Read more
Online Divorce in Oregon: A Step-by-Step Guide...
«Marriage is not super-important to me - most end in divorce. I love the idea of being ...
Read more
Fashion Forever: Discover How to Look Fabulous at Any Age...
In the fast-paced and ever-changing world of fashion, age has often been considered ...
Read more
Cybersecurity Attacks You Should Know to Protect Yourself...
Cybersecurity refers to the set of practices, technologies, and processes designed t...
Read more
The Evolution of Women's Fashion: From Corsets to Personal Expres...
Women's fashion is a vivid reflection of cultural, social, and political evolution t...
Read more
Challenging the Speed of Sound: In the Footsteps of the Fastest A...
Since the dawn of human civilization, the desire to fly has been a fascination deepl...
Read more
Transform Your Home into a Sanctuary of Beauty: Tips for Creating...
Home is much more than just four walls and a roof. It is a refuge, a place where we ...
Read more
Life After Death 2.0: The Technological Revolution of 'Upload'...
In the digital era we live in, the concept of life after death has taken an unexpect...
Read more1
Selected for You

What does the color green mean? The eternal shade of tranquility...
In the vast spectrum of colors that paint our world, green stands out as a hue that ...
Read more
Fashion that Inspires: Brands that Transform Messages into Empowe...
Fashion, beyond being a mere aesthetic expression, has become a powerful tool to emp...
Read more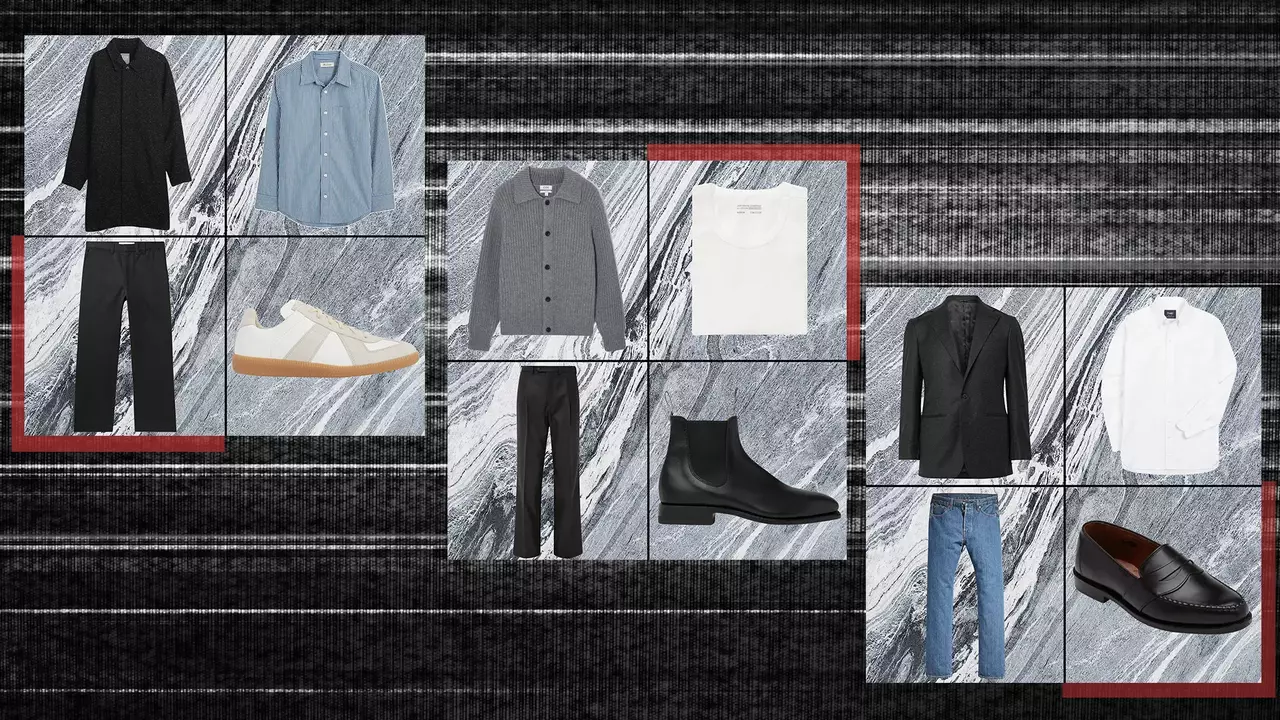
The Ultimate Guide to Creating a Capsule Wardrobe...
In a world where fashion is ever-changing and the abundance of choices can be overwh...
Read more
Stripes, Flowers, and Checks: The Visual Palette of Modern Fashio...
Patterns have played a crucial role in the fashion industry, transforming simple gar...
Read more
The Enigma of No. 6: Technology, Utopia, and Its Hidden Secrets...
Technology has long been envisioned as a means to create utopian societies, where ef...
Read more
Fashion Forever: Discover How to Look Fabulous at Any Age...
In the fast-paced and ever-changing world of fashion, age has often been considered ...
Read more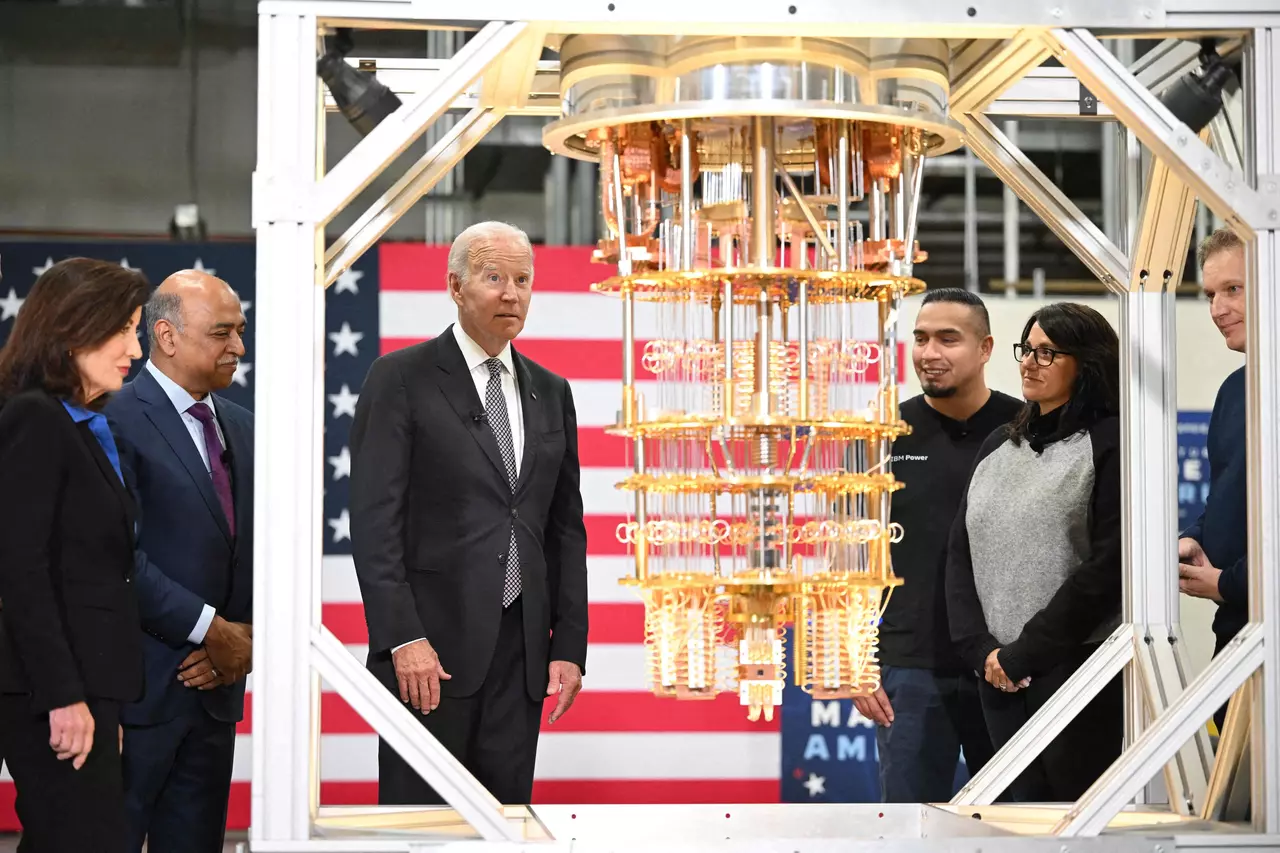
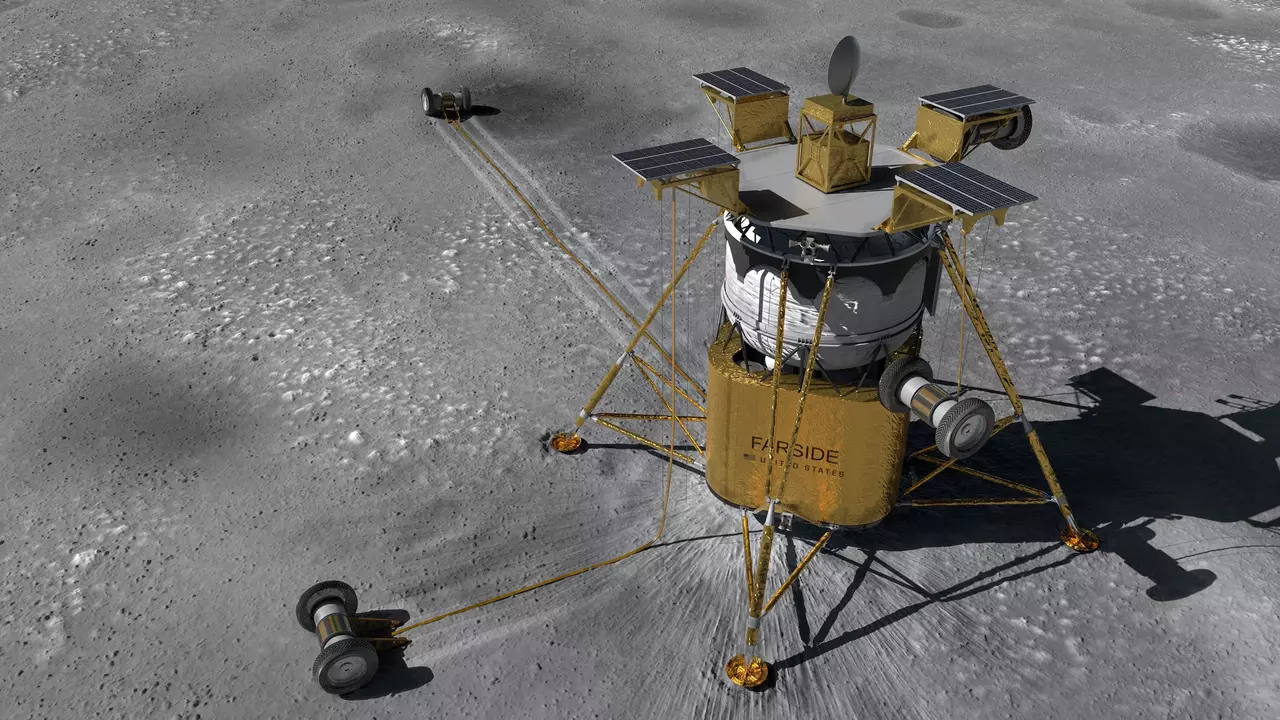
The Quantum Leap: IBM Announces Its Star Machine in San Sebastián...
In the ever-evolving landscape of computing, there is a groundbreaking technological...
Read more
Traveling with Elegance: Fashion Looks for Destinations and Journ...
Fashion traveling is more than just packing a suitcase; it's a lifestyle, a form of ...
Read more